Today I noticed that all of the files that I had saved on the desktop in Windows 7 were gone. The only icon that I saw on the desktop was the Recycle Bin. Since I needed to access the files, I started to investigate the issue. First thing that I did check was to make sure that I had not unchecked the show desktop files option. I verified that despite the fact that I saw the Recycle Bin icon on the desktop.
The option to show desktop icons was checked, so that was not it. Next thing on the list was to search for the files on the system, which turned up that they were not anymore on it. I also fired up Office 2013 to load some of the recent files but that did result in an error message that the documents could not be found on the system, and that I should check whether they had been moved.
Research on the Internet showed me that I was not the only user with the issue. Not all issues were resolved in the various forum threads on the Internet, but some solutions included scanning the file with up to date antivirus software to make sure that malware was not to blame for the disappearance of files on the desktop.
Scans with Malwarebytes Anti-Malware and Dr. Web Cure It did not find malware on the system that could have been responsible for the removal of the desktop files.
Next try System Restore. I had multiple System Restore points at my disposal. The last ones were created after Windows Updates, the installation of the ramdisk software, and SlimCleaner.
I restored the points but the desktop items did not return. Last chance file recovery right? Recuva found some of the documents but not all. I was about to give up when I decided to browse some of the System Restore points just to find out if one of them had the documents listed. They should have, considering that I have been working with the documents yesterday.
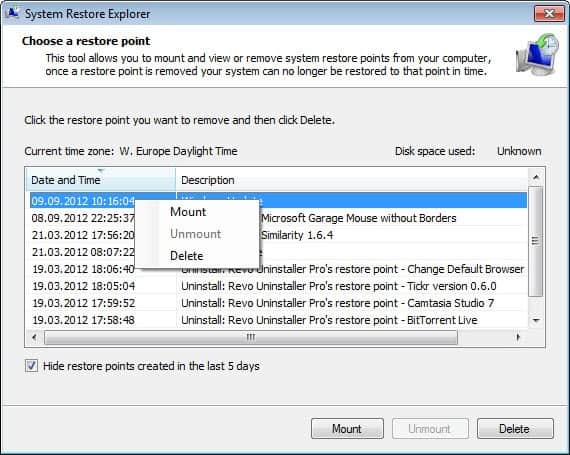
I have used System Restore Explorer for that. You can use the program to mount system restore points so that you can browse and restore individual files.
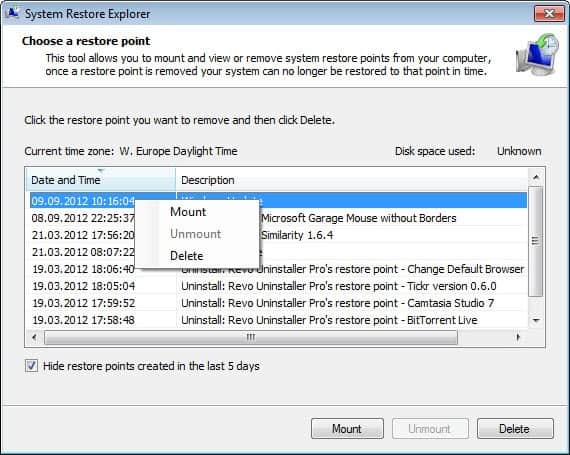
And guess what, the first system restore backup that I mounted contained the files and folders that I had stored on the desktop. I’m not entirely sure why the files have not been recovered when I restored the backup that contained them though. It could be a issue with files on the desktop, but that is just a guess. I can create new icons and files on the desktop, and they remain there even after reboots.

I already did a sfc /scannow on the console to make sure that no important files were corrupted that caused this. I also checked the disk which required no repairs as well.
If you have an idea what could have caused this let me know please, I’d really like to find an answer for the issue. I’m also not sure why restoring the System Restore point did not restore the files on the desktop, as they were included in the backup.
Original article at Ghacks



 Nikto is an open source web server scanner which performs comprehensive tests against web servers for multiple items, including over 6500 potentially dangerous files/CGIs, checks for outdated versions…
Nikto is an open source web server scanner which performs comprehensive tests against web servers for multiple items, including over 6500 potentially dangerous files/CGIs, checks for outdated versions…